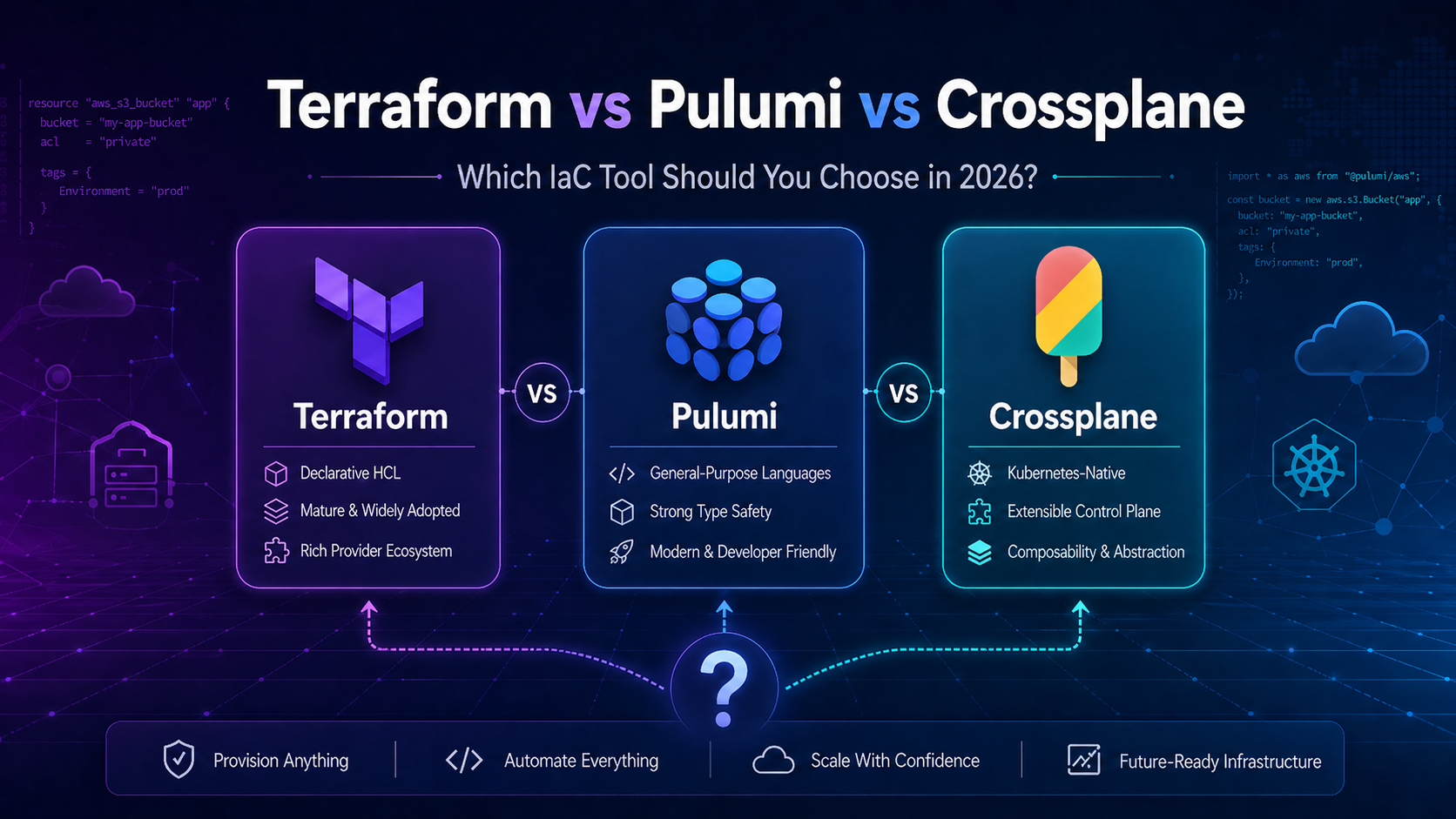
The Infrastructure as Code landscape has changed dramatically. Terraform's license change spawned OpenTofu. Pulumi matured into a serious contender. Crossplane graduated from CNCF incubator and is now the default choice for Kubernetes-native platform teams.
If you're building an Internal Developer Platform, or just trying to pick the right IaC tool, this comparison will help you decide.
Quick Comparison
| Terraform | Pulumi | Crossplane | |
|---|---|---|---|
| Language | HCL (DSL) | TypeScript, Python, Go, C#, Java | YAML + Go (providers) |
| Model | Plan/Apply | Plan/Apply (language SDK) | Continuous Reconciliation |
| Requires K8s? | No | No | Yes |
| Providers | 3,500+ | 3,500+ (via bridge) | Smaller, growing |
| Learning Curve | Moderate | Moderate (devs) | Steep |
| GitOps Fit | Moderate | Moderate | Excellent |
| Drift Detection | At plan time | At plan time | Continuous (auto-correct) |
Terraform: The Industry Standard
Terraform is the safe choice. It's been around since 2014, has the largest provider ecosystem, and is backed by HashiCorp's $6.4B valuation.
Strengths:
- HCL is accessible. Both developers and ops engineers can read and write it. No programming background required.
- Plan/apply workflow. You always see what will change before it changes. This is Terraform's killer feature.
- Mature collaboration patterns. Remote state, state locking, workspaces, PR-based review, all battle-tested.
- Massive ecosystem. If there's a cloud service, there's a Terraform provider for it.
Weaknesses:
- HCL is limited. No real loops, conditionals, or abstractions. Complex logic means
count,for_each, anddynamicblock gymnastics. - State file pain. The state file is a single point of failure. Losing it means losing track of your infrastructure.
- No native drift correction. You catch drift during the next
terraform plan. If someone changed something in the console last week, you won't know until you runplan.
Best for: Most teams. If you need broad provider coverage without a dedicated platform team, start here.
Pulumi: Infrastructure as Real Code
Pulumi takes a fundamentally different approach: write infrastructure in general-purpose programming languages. TypeScript, Python, Go, C#, Java, pick your language.
Strengths:
- Real programming constructs. Loops, classes, functions, inheritance, package managers. No HCL workarounds.
- Superior IDE experience. Autocomplete, type checking, refactoring, debugging, all the things you get when writing real code.
- Test with standard frameworks. Unit test your infrastructure with Jest, pytest, or Go's testing package.
- No context switching. Developers write infrastructure in the same language as their application.
Weaknesses:
- Flexibility can backfire. Without discipline, IaC codebases become unstructured monoliths.
- Smaller native ecosystem. Pulumi bridges Terraform providers, which works but adds a translation layer.
- Steeper for ops teams. If your team doesn't write application code daily, Pulumi's developer-centric approach is a harder sell.
Best for: Developer-heavy teams building complex, multi-environment platforms.
Crossplane: Kubernetes-Native Control Plane
Crossplane isn't just another IaC tool, it's a fundamentally different model. Instead of plan/apply, it uses Kubernetes controllers to continuously reconcile your infrastructure to the desired state.
Strengths:
- Continuous reconciliation. If someone deletes your S3 bucket, Crossplane recreates it. Automatically. No
terraform planrequired. - Compositions. Build curated, product-like APIs. Instead of "create an RDS instance with these 15 parameters," developers request an
AppDatabase, and Crossplane handles the rest. - Native GitOps. ArgoCD or Flux watches your manifests, Crossplane reconciles infrastructure. Perfect fit.
- True self-service. The platform team defines what's allowed. Developers self-serve within those guardrails.
Weaknesses:
- Requires a Kubernetes cluster. You need K8s running before you can provision anything else. This is the chicken-and-egg problem.
- Requires deep Kubernetes expertise. CRDs, controllers, RBAC, debugging distributed failures, you need to know K8s well.
- YAML is verbose. Even with Compositions, you're writing a lot of YAML. Helm and Kustomize become necessary for real-world use.
- Slower time to value. You can't just start provisioning. You need to design the platform first.
Best for: Organizations with dedicated platform teams that are already Kubernetes-centric.
Decision Framework
Pick Terraform if:- You need broad provider coverage
- Your team includes ops engineers who don't write application code
- You want the fastest time to value
- You need the plan/apply safety net
- Your team is developer-heavy
- You need complex, dynamic infrastructure logic
- You want to use standard testing frameworks for IaC
- HCL is holding you back
- You have a dedicated platform team
- Kubernetes is already central to your operation
- You want continuous reconciliation and self-service APIs
- You're willing to invest in platform design upfront
The Hybrid Approach (What Large Orgs Actually Do)
Here's something most comparison posts won't tell you: many large organizations use both Terraform and Crossplane.
Terraform provisions the foundational infrastructure (VPCs, K8s clusters, IAM, networking). Crossplane runs inside those clusters, providing developer-facing abstractions (databases, buckets, queues) through Compositions.
This pattern gives you the best of both worlds: Terraform's broad ecosystem for Day 0 infrastructure, Crossplane's self-service APIs for Day 1+.
Getting Started With Each Tool
If you want hands-on experience with these tools, here's where to start:
- Terraform 004 covers the HashiCorp Terraform Associate certification with hands-on labs, available for AWS, Azure, and GCP. AWS · Azure · GCP
- Crossplane 101 teaches you providers, managed resources, compositions, and XRD patterns, everything you need to build a Kubernetes-native control plane. Learn more
Both courses are included in TeKanAid Premium, along with Vault Associate 003, Backstage 101, and the 21-week Platform Engineering Bootcamp.
Get the Terraform Workflow Checklist
A step-by-step checklist for every Terraform project, from init to destroy. Free when you subscribe.